Protect your organisation by protecting its data.
The last 12 months have brought higher levels of data protection disruption for organisations as the experience of cyberattacks or incidents has become more prevalent. Having a cyber recovery strategy has become a mandate for IT decision makers, yet many organisations lack confidence in their data protection solutions.
Backup is not enough
Cyberattacks are designed to destroy, steal or otherwise compromise your valuable data - including your backups. Immutability preserves the original integrity of your critical data. Multiple layers of security and controls protect against destruction, deletion and alteration. Physical and logical isolation of your critical data complements immutability by providing an additional layer of protection. Unless your backup is stored with immutability and ideally isolated, it remains at risk.
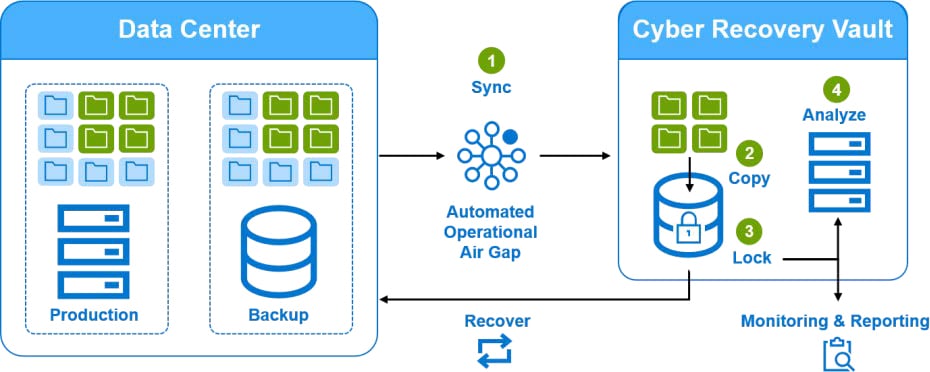
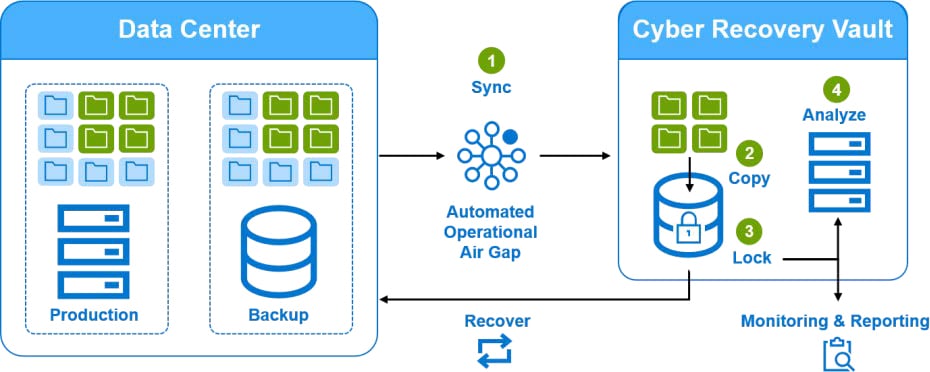
Dell Cyber Recovery Vault
The Dell PowerProtect Cyber Recovery vault automates the synchronisation of data between production systems and the vault creating immutable copies with locked retention policies. Additional safeguards include an automated operational air gap to provide network isolation and eliminate management interfaces which could be compromised. If a cyberattack occurs you can quickly identify a clean copy of data, recover your critical systems and get your business back up and running.